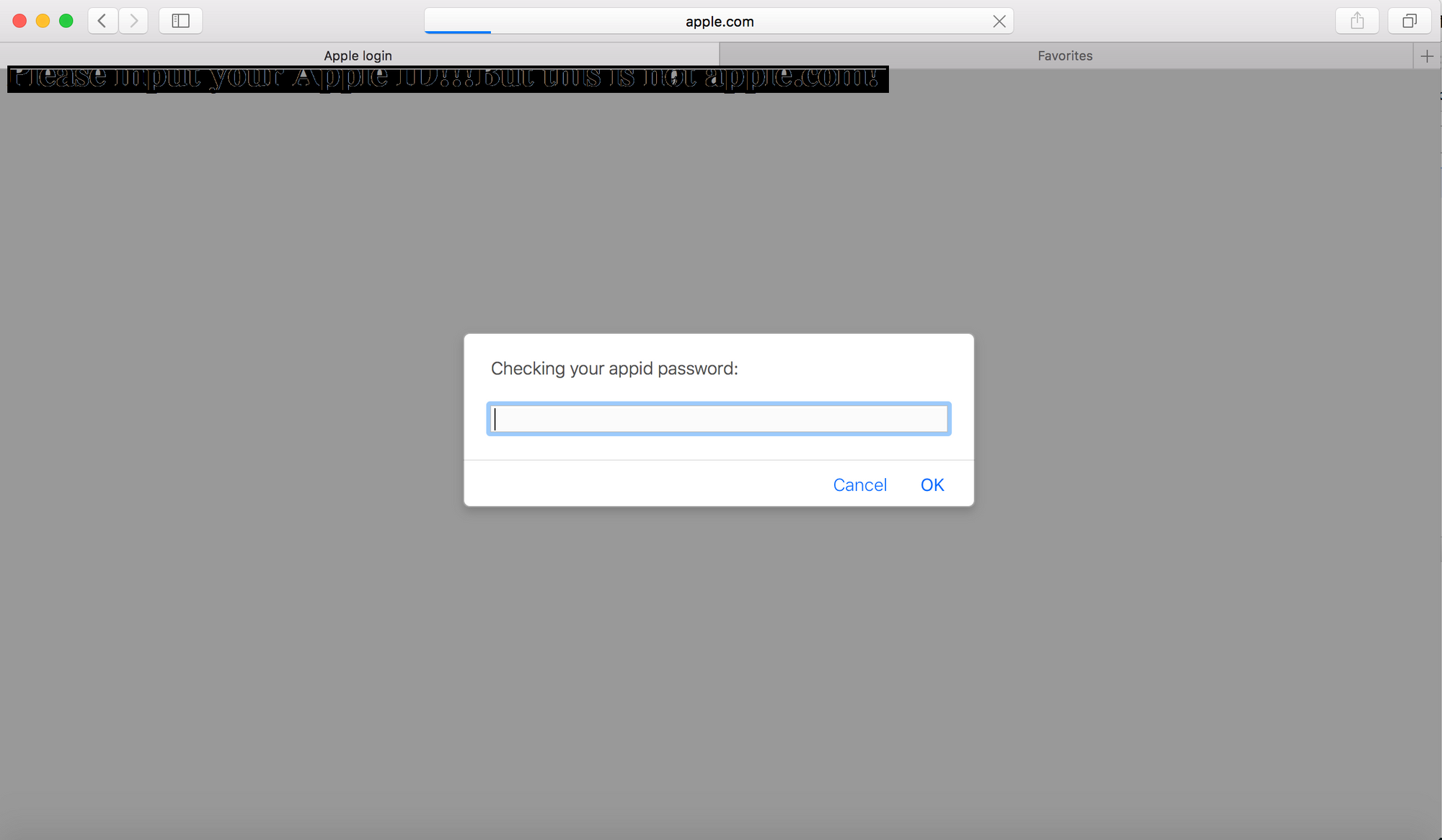
(CVE-2017-2500)Address bar spoofing on macOS Safari
Affected Products
Safari <10.1.1 on macOS
Description
When we input an URL including a special port or visit a domain which exists in DNS record but cannot access anymore (such as “http://www.apple.com:1234" or “http://access.apple.com"), Safari will try its best to load this address, so address bar spoofing could occur during the loading time!
Proof of concept
1 | <script> |
Disclosure Timelines
2017/2/7 Provide vulnerability detail to APPLE via product-security@apple.com
2017/4/26 Apple fix it in Safari 10.1.1
2017/5/12 CVE-2017-2500 assigned.
Credit
This vulnerability was discovered by Zhiyang Zeng and Yuyang Zhou of Tencent Security Platform Department.